Information privacy
{{Short description|Legal issues regarding the collection and dissemination of data}} {{distinguish|Data security}}
'''Information privacy''', also known as '''data privacy''' or '''data protection''', is the relationship between the collection and dissemination of [[data]], [[technology]], the public [[expectation of privacy]], [[Contextual integrity|contextual information norms]], and the [[legal]] and [[political]] issues surrounding them.{{Cite book |title=Uberveillance and the social implications of microchip implants : emerging technologies |others= |date=30 September 2013 |isbn=978-1466645820 |location=Hershey, PA |oclc=843857020|last=Michael|first=M. G.|last2=Michael|first2=Katina|url=https://www.google.com/books/edition/Uberveillance_and_the_Social_Implication/oI2GAgAAQBAJ?hl=en&gbpv=1&pg=PA259&printsec=frontcover|pages=259}}
Various types of [[Personal Information|personal information]] often come under privacy concerns. [[Privacy]] concerns exist wherever [[personally identifiable information]] or other [[Information sensitivity|sensitive information]] is collected, stored, used, and finally destroyed or deleted – in [[Digital data|digital form]] or otherwise. Improper or non-existent disclosure control can be the root cause for privacy issues. [[Informed consent]] mechanisms including [[Privacy policy|privacy policies]] and [[dynamic consent]] are important in communicating to data subjects the different uses of their personally identifiable information.
== History == In 1890, legal scholars [[Samuel D. Warren II]] and [[Louis Brandeis]] published "[[The Right to Privacy (article)|The Right to Privacy]]", an article explaining "the right to be let alone," which helped establish a [[right to privacy]] in the United States.{{Cite journal |last=Solove |first=Daniel J. |date=2006 |title=A Taxonomy of Privacy |url=https://www.jstor.org/stable/40041279 |journal=University of Pennsylvania Law Review |volume=154 |issue=3 |pages=477–564 |doi=10.2307/40041279 |issn=0041-9907}} Their guidelines set the foundation for how privacy can be understood in terms of personal data, and influenced the development of the [[privacy laws of the United States]].
In the United States, the [[Privacy Act of 1974]] represented an achievement in [[information privacy law]]. The law set a Code of Fair Information Practice to govern how federal agencies collect personal information and data. After the [[Watergate scandal|Watergate]] and [[COINTELPRO]] scandals involving illegal government use of [[surveillance]], this privacy law was intended to help restore [[public trust]] in the government.{{Cite web |date=2020-10-14 |title=Overview of The Privacy Act of 1974 (2020 Edition) - Introduction |url=https://www.justice.gov/opcl/overview-privacy-act-1974-2020-edition/introduction |access-date=2026-02-08 |website=U.S. Department of Justice, Office of Privacy and Civil Liberties |language=en}} The Act allowed a person to have the right to access information about themselves and know how their information would be used.{{Cite web |title=Privacy Act of 1974, 5 U.S.C. § 552a {{!}} Bureau of Justice Assistance |url=https://bja.ojp.gov/program/it/privacy-civil-liberties/authorities/statutes/1279 |access-date=2025-12-03 |website=bja.ojp.gov |language=en}}{{Cite web |last=Stuessy |first=Meghan M. |date=2023-12-07 |title=The Privacy Act of 1974: Overview and Issues for Congress |url=https://www.congress.gov/crs-product/R47863 |access-date=2025-12-03 |website=Congressional Research Service - Congress.gov}}
The growth of the internet's popularity in the early 2000s presented different privacy concerns as many companies and organizations began to collect user's personal data. Scholars such as [[Daniel J. Solove|Daniel Solove]] explained the importance of [[informed consent]].{{Cite journal |last=Solove |first=Daniel J. |date=2006 |title=A Taxonomy of Privacy |url=https://www.jstor.org/stable/40041279 |journal=University of Pennsylvania Law Review |volume=154 |issue=3 |pages=477–564 |doi=10.2307/40041279 |issn=0041-9907}}
In 2018, the [[Facebook–Cambridge Analytica data scandal]] introduced new privacy risks to the public. A consulting firm called Cambridge Analytica collected personal user data from over 85 million Facebook users without informed consent.{{Cite web |last=visceral_dev_admin |date=2023-03-16 |title=History of the Cambridge Analytica Controversy |url=https://bipartisanpolicy.org/article/cambridge-analytica-controversy/ |access-date=2025-12-03 |website=Bipartisan Policy Center |language=en-US}} The data collected was used to assist in politically targeted ads during the [[2016 United States presidential election|2016 U.S. presidential election]]. This resulted in the United States Federal Trade Commission fining Facebook $5 billion.{{Cite news |last=Zialcita |first=Paolo |date=2019-10-30 |title=Facebook Pays $643,000 Fine For Role In Cambridge Analytica Scandal |url=https://www.npr.org/2019/10/30/774749376/facebook-pays-643-000-fine-for-role-in-cambridge-analytica-scandal |access-date=2025-12-03 |work=NPR |language=en}}{{Cite web |last=Reynolds |first=Taylor |date=2018-03-20 |title=Facebook/Cambridge Analytica: Privacy lessons and a way forward |url=https://internetpolicy.mit.edu/blog-2018-fb-cambridgeanalytica/ |access-date=2025-12-03 |website=Internet Policy Research Initiative at MIT |language=en-US}} The Cambridge Analytica scandal influenced new legislation such as the European Union's [[General Data Protection Regulation]].
== Types of information privacy == Data privacy issues may arise in response to information from a wide range of sources, such as:{{Cite book|title=Programme Management Managing Multiple Projects Successfully.|date=2009|publisher=Global India Pubns|others=Mittal, Prashant.|isbn=978-9380228204|oclc=464584332}}
- [[Electronic health record|Healthcare records]]
- [[Criminal justice]] investigations and proceedings
- [[Financial]] institutions and transactions
- [[Biological]] traits, such as [[genetic material]]
- [[house|Residence]] and geographic records
- [[Privacy breach]]
- [[Location-based service]] and [[geolocation]]
- [[Behavioral Targeting|Web surfing behavior]] or user preferences using [[persistent cookie]]s
- [[Academic research]]
===Financial=== {{Main|Financial privacy}}
Information about a person's financial transactions, including the amount of assets, positions held in stocks or funds, outstanding debts, and purchases can be sensitive. If criminals gain access to information such as a person's accounts or credit card numbers, that person could become the victim of [[fraud]] or [[identity theft]]. Information about a person's purchases can reveal a great deal about that person's history, such as places they have visited, whom they have contact with, products they have used, their activities and habits, or medications they have used. In some cases, corporations may use this information to [[Targeted advertising|target]] individuals with [[marketing]] customized towards those individual's personal preferences, which that person may or may not approve.{{cite news |last=Fiveash |first=Kelly |date=2012-11-08 |title=Psst: Heard the one about the National Pupil Database? Thought not |url=https://www.theregister.co.uk/2012/11/08/national_pupil_database_regulation_overhaul_in_private_sector_data_grab/ |access-date=2012-12-12 |work=[[The Register]]}}
===Internet=== {{Main|Internet privacy}}
The ability to control the information one reveals about oneself over the internet and who can access that information has become a growing concern. These concerns include whether [[email]] can be stored or read by third parties without consent or whether third parties can continue to track the websites that someone visited. Another concern is whether websites one visits can collect, store, and possibly share [[personally identifiable information]] about users.
The advent of various [[Web search engine|search engines]] and the use of [[data mining]] created a capability for data about individuals to be collected and combined from a wide variety of sources very easily.{{cite news|url=https://www.usatoday.com/tech/news/surveillance/2006-06-18-data-mining-privacy_x.htm|title=Research explores data mining, privacy|last=Bergstein|first=Brian|date=2006-06-18|work=USA Today|access-date=2010-05-05}}{{cite news|url=http://www.seattlepi.com/business/154986_privacychallenge02.html|title=In this data-mining society, privacy advocates shudder|last=Bergstein|first=Brian|date=2004-01-01|work=Seattle Post-Intelligencer}}{{cite news|url=http://connection.ebscohost.com/c/articles/21472572/u-s-demands-google-web-data|archive-url=https://web.archive.org/web/20141219105358/http://connection.ebscohost.com/c/articles/21472572/u-s-demands-google-web-data|url-status=dead|archive-date=2014-12-19|title=U.S. Demands Google Web Data|last=Swartz|first=Nikki|work=Information Management Journal|year=2006}} Vol. 40 Issue 3, p. 18 AI facilitated creating inferential information about individuals and groups based on such enormous amounts of collected data, transforming the information economy. {{cite book|last1=Cofone |first1=Ignacio |title=The Privacy Fallacy: Harm and Power in the Information Economy|url = https://www.cambridge.org/core/books/privacy-fallacy/547578F2A1AE0C40963105CE066B412E |publisher=Cambridge University Press |year=2023 |isbn=9781108995443 |location=New York }} The FTC has provided a set of guidelines that represent widely accepted concepts concerning fair information practices in an electronic marketplace, called the [[Fair Information Practice Principles]]. But these have been critiqued for their insufficiency in the context of AI-enabled inferential information.
On the internet many users give away a lot of information about themselves: unencrypted emails can be read by the administrators of an [[e-mail server]] if the connection is not encrypted (no [[Transport Layer Security|TLS]]), and also the [[internet service provider]] and other parties [[packet analyzer|sniffing]] the network traffic of that connection are able to know the contents. The same applies to any kind of traffic generated on the Internet, including [[web browsing]], [[instant messenger|instant messaging]], and others. In order not to give away too much personal information, emails can be encrypted and browsing of webpages as well as other online activities can be done anonymously via [[anonymizer]]s, or by open source distributed anonymizers, so-called [[mix network]]s. [[The Nym mixnet|Nym]]{{Cite web|url=https://nym.com/nym-whitepaper.pdf|title=Nym Mixnet Whitepaper}} and [[I2P]]{{Cite web|url=https://geti2p.net/en/docs/how/threat-model|access-date=2025-05-07 |title=I2P's Threat Model - I2P }} are examples of well-known [[mixnet|mix nets]].
With social media and e-commerce sites being used more frequently, there are more potential openings for stealing consumer’s data. Companies can see which types of products consumers like to purchase and can use targeted ads to try to make people purchase more items thinking that this is what they will want to purchase. However, sometimes this type of data is used without explicit consent.Federal Trade Commission. (2022). ''Protecting Consumer Privacy in an Era of Rapid Change.'' Retrieved from https://www.ftc.gov/reports
Users are unaware of all of the personal information that is collected about them. Cookies track browsing data and location settings show where a person is based out of, and can show shops or products that are physically located near someone.Smith, A. (2023). ''Tracking, cookies, and digital privacy: Understanding online data collection.'' Journal of Cyber Policy, 8(1), 45–61. These combined that be a big safety and privacy issue for users if their data is not being stored safely.
With laws like the [[California Consumer Privacy Act]] (CCPA), people’s data can be protected and they asked for explicit consent before using said data.California Legislative Information. (2020). ''California Consumer Privacy Act (CCPA)''. Retrieved from https://leginfo.legislature.ca.gov/faces/codes_displayText.xhtml?division=3.&part=4.&lawCode=CIV Globally, many nations are trying to implement similar clauses to protect consumers.
Email is not the only internet content with privacy concerns. In an age where increasing amounts of information are online, social networking sites pose additional privacy challenges. People may be tagged in photos or have valuable information exposed about themselves either by choice or unexpectedly by others, referred to as [[participatory surveillance]]. Data about location can also be accidentally published, for example, when someone posts a picture with a store as a background. Caution should be exercised when posting information online. Social networks vary in what they allow users to make private and what remains publicly accessible.{{cite book|url=https://books.google.com/books?id=E1fQdrzxAPoC&pg=PA17-IA137|title=The Internet: Illustrated Series|author=Schneider, G.|author2=Evans, J.|author3=Pinard, K.T.|publisher=Cengage Learning|year=2008|isbn=9781423999386|page=156|access-date=9 May 2018}} Without strong security settings in place and careful attention to what remains public, a person can be profiled by searching for and collecting disparate pieces of information, leading to cases of [[cyberstalking]]{{cite book|title=Cyberstalking: Harassment in the Internet Age and How to Protect Your Family|author=Bocij, P.|publisher=Greenwood Publishing Group|year=2004|isbn=9780275981181|pages=[https://archive.org/details/cyberstalkinghar00boci/page/268 268]|url-access=registration|url=https://archive.org/details/cyberstalkinghar00boci/page/268}} or reputation damage.{{cite book|url=https://books.google.com/books?id=tGC_DQAAQBAJ&pg=PA26|title=Privacy, free expression and transparency: Redefining their new boundaries in the digital age|author=Cannataci, J.A.|author2=Zhao, B.|author3=Vives, G.T.|publisher=UNESCO|year=2016|isbn=9789231001888|page=26|display-authors=etal|access-date=9 May 2018}}
Cookies are used on websites so that users may allow the website to retrieve some information from the user's internet, but they usually do not mention what the data being retrieved is.{{Cite journal| author1=Bornschein, R.| author2=Schmidt, L.| author3=Maier, E.| author4=Bone, S. A.| author5=Pappalardo, J. K.| author6=Fitzgerald, M. P.| date=April 2020| title=The Effect of Consumers' Perceived Power and Risk in Digital Information Privacy: The Example of Cookie Notices| journal=Journal of Public Policy & Marketing| language=en| volume=39|issue=2 | pages=135–154| doi=10.1177/0743915620902143|s2cid=213860986| issn=0743-9156| doi-access=free}} In 2018, the General Data Protection Regulation (GDPR) passed a regulation that forces websites to visibly disclose to consumers their information privacy practices, referred to as cookie notices. This was issued to give consumers the choice of what information about their behavior they consent to letting websites track; however, its effectiveness is controversial. Some websites may engage in deceptive practices such as placing cookie notices in places on the page that are not visible or only giving consumers notice that their information is being tracked but not allowing them to change their privacy settings. Apps like Instagram and Facebook collect user data for a personalized app experience; however, they track user activity on other apps, which jeopardizes users' privacy and data. By controlling how visible these cookie notices are, companies can discreetly collect data, giving them more power over consumers.
===Educational=== In the United Kingdom in 2012, the Education Secretary [[Michael Gove]] described the [[National Pupil Database]] as a "rich dataset" whose value could be "maximised" by making it more openly accessible, including to private companies. Kelly Fiveash of ''[[The Register]]'' said that this could mean "a child's school life including exam results, attendance, teacher assessments and even characteristics" could be available, with third-party organizations being responsible for anonymizing any publications themselves, rather than the data being anonymized by the government before being handed over. An example of a data request that Gove indicated had been rejected in the past, but might be possible under an improved version of privacy regulations, was for "analysis on sexual exploitation".
===Cable television=== This describes the ability to control what information one reveals about oneself over cable television, and who can access that information. For example, third parties can track [[Internet Protocol television|IP TV]] programs someone has watched at any given time.{{Citation needed|date=February 2026}}
=== Academic research === Within academia, [[Institutional review board|Institutional Review Boards]] function to assure that adequate measures are taken to ensure both the privacy and confidentiality of human subjects in research.{{Cite web |date=October 5, 2017 |title=Institutional Review Board - Guidebook, CHAPTER IV - CONSIDERATIONS OF RESEARCH DESIGN |url=https://www.hhs.gov/ohrp/education-and-outreach/archived-materials/index.html |access-date=October 5, 2017 |website=www.hhs.gov}}
== Data breaches and privacy risks == When an individual or group of people steal consumer’s data it is considered a breach of data. It is a common threat to one’s information privacy. This includes information such as names, date of birth, credit card information, and social security numbers.{{Cite web |title=2025 Data Breach Investigations Report |url=https://www.verizon.com/business/resources/reports/dbir/ |access-date=2025-12-03 |website=Verizon Business}}
These types of data breaches can happen when companies do not have the most current or secure infrastructure to secure and encrypt data. A small gap can open data to being leaked from outsiders. It should also be noted that breaches can happen from inside employees exposing information too.{{Cite web |title=Cost of a data breach 2025 {{!}} IBM |url=https://www.ibm.com/reports/data-breach |access-date=2025-12-03 |website=www.ibm.com |language=en}} Companies are investing time in teaching about suspicious activity and using multi factor authentication systems.
On a federal level in Europe, governments are now mandating that companies report breaches in a timely manner.European Parliament. (2016). ''General Data Protection Regulation (GDPR), Regulation (EU) 2016/679.'' In America HIPAA functions in a similar way and notifies patients when data has been exposed U.S. Department of Health and Human Services. (2021). ''Health Information Privacy.'' Retrieved from https://www.hhs.gov/hipaa/index.html With types of guidelines in place, companies and countries are working to protect personal information and explain how personal data can and should be used.
Laws surrounding information privacy are important for protecting information globally. This includes laws that ensure data is collected with consent and is used with transparency .Organisation for Economic Co-operation and Development (OECD). (2013). ''The OECD Privacy Framework.'' Retrieved from https://www.oecd.org/sti/privacy-framework.htmUnited Nations. (2018). ''Personal Data Protection and Privacy Principles.'' Retrieved from https://www.un.org/en/dataprivacy
In the continent of Europe, a guideline called The European Union’s General Data Protection Regulation requires everyone to ask for consent before using consumer data and to limit the amount of data companies need to take from users in general.European Parliament. (2016). ''General Data Protection Regulation (GDPR), Regulation (EU) 2016/679.'' The European Union’s General Data Protection Regulation has shown success, and has prompted other nations to follow suit. For example, the state of California and the country of Canada decided to create and implement their own version of the European Union’s General Data Protection Regulation. California created the California Privacy Rights Act (CPRA, 2020) and Canada created the PIPEDA (Government of Canada, 2021), both modeling their guidelines on The European Union’s General Data Protection Regulation that puts consumer and user data and privacy right’s first.California Legislative Information. (2020). ''California Consumer Privacy Act (CCPA).'' Retrieved from https://leginfo.legislature.ca.gov/faces/codes_displayText.xhtml?division=3.&part=4.&lawCode=CIVGovernment of Canada. (2021). ''Personal Information Protection and Electronic Documents Act (PIPEDA).'' Retrieved from https://www.priv.gc.ca/en/
More broadly, the U.S. collectively is still working on creating a comprehensive program that can protect data within the many sectors of jobs and companies operating out of the U.S. However, there are smaller guidelines and policies for each organization. For example, HIPAA or [[Health Insurance Portability and Accountability Act]] protects medical patient data and information U.S. Department of Health and Human Services. (2021). ''Health Information Privacy.'' Retrieved from https://www.hhs.gov/hipaa/index.html This is not on a national level that protects all user data from different types of companies, but in the U.S. there are organization and industry level protections created.
=== Artificial intelligence and privacy === Artificial intelligence can be seen as a hindrance to protecting information privacy as they collect data widely. According to the International Association of Privacy Professionals, about 68% of consumers globally express concern about their privacy online with 57% agreeing that AI can be a threat to their data.International Association of Privacy Professionals. (2023). "Consumer Perspectives of Privacy and Artificial Intelligence." https://iapp.org/resources/article/consumer-perspectives-of-privacy-and-ai/ These concerns have intensified as generative AI tools, which learn from data scraped from the web, have become more widely adopted.
AI privacy concerns can be linked to unregulated data collection methods, opaque algorithms, and data persistence.RAND Corporation. (2024). "Artificial Intelligence Impacts on Privacy Law." https://www.rand.org/pubs/research_reports/RRA3243-2.html Algorithmic opacity means not understanding exactly how and where AI is getting their data and sources from.. The lack of clear visibility can make it difficult for someone to understand how their information is being found and used. Data persistence is data existing for an extended period of time online that can also be without consent.
As of now in the United States there are not any explicit federal laws governing AI in terms of data collection.Congressional Research Service. "Generative Artificial Intelligence and Data Privacy: A Primer." https://www.congress.gov/crs-product/R47569 Laws such as the Health Insurance Portability and Accountability Act (HIPAA) and Gramm Leach Bliley Act can regulate companies but it excludes AI. There are state legislatures being enacted. The state of Utah in the United States passed the Artificial Intelligence Policy Act in March of 2024.IBM. (2024). "Exploring Privacy Issues in the Age of AI." https://www.ibm.com/think/insights/ai-privacy The White House Office of Science and Technology Policy created the "Blueprint for an AI Bill of Rights" in 2022 which explained frameworks for data privacy and AI and having AI systems collect user consent prior to using their data.
Many researchers have created additional frameworks to address AI and data privacy including data minimization requirements, auditing of AI, and giving users an option to opt out of data collection when using AI.Stanford University Human-Centered Artificial Intelligence. "Privacy in an AI Era: How Do We Protect Our Personal Information?" https://hai.stanford.edu/news/privacy-ai-era-how-do-we-protect-our-personal-information
===Locational=== As location tracking capabilities of mobile devices are advancing ([[location-based service]]s), problems related to user privacy arise. [[Location data]] is among the most sensitive data currently being collected.{{cite book |chapter-url=https://books.google.com/books?id=_BdADQAAQBAJ&pg=PA360 |title=Progress in Location-Based Services 2016 |chapter=Ephemerality Is the New Black: A Novel Perspective on Location Data Management and Location Privacy in LBS |author=Ataei, M. |author2=Kray, C. |publisher=Springer |pages=357–374 |year=2016 |isbn=9783319472898 |access-date=9 May 2018}} A list of potentially sensitive professional and personal information that could be inferred about an individual knowing only their mobility trace was published in 2009 by the [[Electronic Frontier Foundation]].{{cite web|last=Blumberg, A. Eckersley, P.|title=On locational privacy and how to avoid losing it forever.|date=3 August 2009|url=https://www.eff.org/wp/locational-privacy|publisher=EFF}} These include the movements of a competitor sales force, attendance of a particular church or an individual's presence in a motel, or at an abortion clinic. A recent MIT study{{cite journal|last=de Montjoye|first=Yves-Alexandre|author2=César A. Hidalgo |author3=Michel Verleysen |author4=Vincent D. Blondel |title=Unique in the Crowd: The privacy bounds of human mobility|journal=Scientific Reports|volume=3|pages=1376|date=March 25, 2013|doi=10.1038/srep01376|pmid=23524645|pmc=3607247|bibcode=2013NatSR...3.1376D}}{{cite news|last=Palmer|first=Jason|title=Mobile location data 'present anonymity risk'|url=https://www.bbc.co.uk/news/science-environment-21923360|access-date=12 April 2013|newspaper=BBC News|date=March 25, 2013}} by de Montjoye et al. showed that four spatio-temporal points, approximate places and times, are enough to uniquely identify 95% of 1.5 million people in a mobility database. The study further shows that these constraints hold even when the resolution of the dataset is low. Therefore, even coarse or blurred datasets provide little anonymity to the person.
===Medical=== {{Main|Medical privacy}}
People may not wish for their medical records to be revealed to others due to the confidentiality and sensitivity of what the information could reveal about their health. For example, they might be concerned that it might affect their insurance coverage or employment. Or, it may be because they would not wish for others to know about any medical or psychological conditions or treatments that would bring embarrassment upon themselves. Revealing medical data could also reveal other details about one's personal life.{{cite journal|last1=Aurelia|first1=Nicholas-Donald|last2=Francisco|first2=Matus, Jesus|last3=SeungEui|first3=Ryu|last4=M|first4=Mahmood, Adam|date=1 June 2017|title=The Economic Effect of Privacy Breach Announcements on Stocks: A Comprehensive Empirical Investigation|url=http://aisel.aisnet.org/amcis2011_submissions/341/|journal=Amcis 2011 Proceedings - All Submissions}} There are three major categories of medical privacy: informational (the degree of control over personal information), physical (the degree of physical inaccessibility to others), and psychological (the extent to which the doctor respects patients' cultural beliefs, inner thoughts, values, feelings, and religious practices and allows them to make personal decisions).{{cite journal|last=Serenko|first=Natalia|author2=Lida Fan|year=2013|title=Patients' Perceptions of Privacy and Their Outcomes in Healthcare|url=https://aserenko.com/IJBHR_Serenko_Fan.pdf|journal=International Journal of Behavioural and Healthcare Research|volume=4|issue=2|pages=101–122|doi=10.1504/IJBHR.2013.057359}} Physicians and psychiatrists in many cultures and countries have standards for [[doctor–patient relationship]]s, which include maintaining confidentiality. In some cases, the [[physician–patient privilege]] is legally protected. These practices are in place to protect the dignity of patients, and to ensure that patients feel free to reveal complete and accurate information required for them to receive the correct treatment.{{cite web|url=http://www.enotes.com/everyday-law-encyclopedia/doctor-patient-confidentiality|title=If a patient is below the age of 18-years does confidentiality still works or should doctor breach and inform the parents?15years girl went for... - eNotes|website=eNotes|access-date=2008-05-29|archive-date=2011-12-02|archive-url=https://web.archive.org/web/20111202122458/http://www.enotes.com/everyday-law-encyclopedia/doctor-patient-confidentiality|url-status=dead}} To view the United States' laws on governing privacy of private health information, see [[Health Insurance Portability and Accountability Act|HIPAA]] and the [[Health Information Technology for Economic and Clinical Health Act|HITECH Act]]. The Australian law is the Privacy Act 1988 Australia as well as state-based health records legislation.
===Children's privacy=== Children's online privacy is subject to legal protections in many ways. In the United States, the Children's Online Privacy Protection Act of 1998 monitors the collection of personal information of children under 13 years of ageFederal Trade Commission. "Children's Online Privacy Protection Rule (COPPA)." https://www.ftc.gov/legal-library/browse/rules/childrens-online-privacy-protection-rule-coppa The law specifically states that website operators must receive parental consent before collecting personal data of children.
The Children's Online Privacy Protection Act of 1998 applies to websites, apps, and all internet based devices that are geared towards children or know that they are collecting data from children under the age of thirteen.Texas Attorney General. "Children's Online Privacy Protection Act (COPPA)." https://www.texasattorneygeneral.gov/consumer-protection/file-consumer-complaint/consumer-privacy-rights/childrens-online-privacy-protection-act Violating this law can result in penalties up to $43,792 per violation as it is enforced by the Federal Trade Commission.Electronic Privacy Information Center. "Children's Privacy." https://epic.org/issues/data-protection/childrens-privacy/ Additionally, there are state attorneys general that enforce this law.
The Federal Trade Commission has continued to update the Children's Online Privacy Protection Act to meet the current update of emerging technology. There was an amendment made in 2013 that expanded the categories of personal information to include persistent identifiers, geolocation data, and any media with a child's description.Federal Trade Commission. (2013). "Revised Children's Online Privacy Protection Rule Goes Into Effect Today." https://www.ftc.gov/news-events/news/press-releases/2013/07/revised-childrens-online-privacy-protection-rule-goes-effect-today The Federal Trade Commisision opened another review of the Children Online Privacy Protection Act in 2019 as well in order to monitor new technologies due to children utilizing mobile devices.
Some have noted that the Children's Online Privacy Protection Act does have its limitations. The law at this time does not prevent children from accessing inappropriate content or lying about their age. Moreover, there have been some doubts regarding how comprehensive the Children's Online Privacy Protection Act with educational technology.
===Political=== {{Main|Political privacy}}
[[Political privacy]] has been a concern since [[voting system]]s emerged in ancient times. The [[secret ballot]] is the simplest and most widespread measure to ensure that political views are not known to anyone other than the voters themselves—it is nearly universal in modern [[democracy]] and considered to be a basic right of [[citizenship]]. In fact, even where other rights of [[privacy]] do not exist, this type of privacy very often does. There are several forms of voting fraud or privacy violations possible with the use of digital voting machines.{{Cite news|url=https://www.nytimes.com/2018/02/21/magazine/the-myth-of-the-hacker-proof-voting-machine.html|title=The Myth of the Hacker-Proof Voting Machine|last=Zetter|first=Kim|date=2018-02-21|work=The New York Times|access-date=2019-04-03|language=en-US|issn=0362-4331}}
==Legality== {{Main|Information privacy law}}
The legal protection of the right to [[privacy]] in general – and of data privacy in particular – varies greatly around the world.{{Cite web|url=http://brooklynworks.brooklaw.edu/cgi/viewcontent.cgi?article=1082&context=bjil|title=Blurred Line: Zooming in on Google Street View and the Global Right to Privacy|last=Rakower|first=Lauren|date=2011|website=brooklynworks.brooklaw.edu|archive-url=https://web.archive.org/web/20171005101128/http://brooklynworks.brooklaw.edu/cgi/viewcontent.cgi?article=1082&context=bjil|archive-date=2017-10-05|url-status=live}} Laws and regulations related to Privacy and Data Protection are constantly changing; it is seen as important to keep abreast of any changes in the law and to continually reassess compliance with data privacy and security regulations.Robert Hasty, Dr Trevor W. Nagel and Mariam Subjally''.'' {{cite web |date=August 2013 |title=Data Protection Law in the USA |url=http://a4id.org/sites/default/files/user/Data%20Protection%20Law%20in%20the%20USA_0.pdf |url-status=dead |archive-url=https://web.archive.org/web/20150925093457/http://www.a4id.org/sites/default/files/user/Data%20Protection%20Law%20in%20the%20USA_0.pdf |archive-date=2015-09-25 |access-date=2013-10-14 |publisher=Advocates for International Development}}
=== Data protection laws === {{main|Information privacy law|Privacy law}}
Data protection laws across the globe aim to secure personal information and safeguard individual privacy in a digital era. The European Union’s General Data Protection Regulation (GDPR) sets a high benchmark, emphasizing consent, transparency, and robust accountability by imposing strict penalties. Many countries adopt similar principles, mandating that organizations implement effective security measures, respect user rights, and notify breaches. In regions such as North America, Asia, and Oceania, data protection frameworks vary from sector-specific regulations to comprehensive legislation. Globally, these laws balance innovation with privacy, ensuring that personal data is appropriately accessible, managed ethically while mitigating misuse and cyber threats.
=== Authorities by country === {{columns-list|colwidth=30em| {{See also|Information commissioner|National data protection authority}}
- [[National data protection authority|National data protection authorities]] in the [[European Union]] and the [[European Free Trade Association]]
- [[Office of the Australian Information Commissioner]] ([[Australia]])
- [[Privacy Commissioner (New Zealand)]]
- {{lang|fr|[[Commission nationale de l'informatique et des libertés]]}} ({{lang|fr|CNIL}}, [[France]])
- [[Federal Commissioner for Data Protection and Freedom of Information]] ([[Germany]])
- [[Office of the Privacy Commissioner for Personal Data]] ([[Hong Kong]])
- [[Data Protection Commissioner]] ([[Republic of Ireland|Ireland]])
- [[Office of the Data Protection Supervisor]] ([[Isle of Man]])
- [[National Privacy Commission (Philippines)]]
- [[Personal Data Protection Act 2012 (Singapore)#Personal Data Protection Commission|Personal Data Protection Commission]] ([[Singapore]])
- [[Turkish Data Protection Authority]] (KVKK, [[Turkey]])
- [[Federal Data Protection and Information Commissioner]] ([[Switzerland]])
- [[Information Commissioner's Office]] (ICO, [[United Kingdom]])
- [[Agencia Española de Protección de Datos]] (AEPD, [[Spain]]) }}
===Safe Harbor program=== {{about|section=yes|the previously invalidated privacy regime|current legal standard|EU-US Data Privacy Framework}} The [[United States Department of Commerce]] created the [[International Safe Harbor Privacy Principles]] certification program in response to the [[Directive 95/46/EC on the protection of personal data|1995 Directive on Data Protection]] (Directive 95/46/EC) of the European Commission.{{cite web |url=http://ec.europa.eu/justice_home/fsj/privacy/law/index_en.htm |title=Protection of personal data |publisher=[[European Commission]] |url-status=dead |archive-url=https://web.archive.org/web/20060616181201/http://ec.europa.eu/justice_home/fsj/privacy/law/index_en.htm |archive-date=16 June 2006 }} Both the United States and the European Union officially state that they are committed to upholding information privacy of individuals, but the former has caused friction between the two by failing to meet the standards of the EU's stricter laws on personal data. The negotiation of the Safe Harbor program was, in part, to address this long-running issue.{{Cite journal |last=Weiss and Archick |first=Martin A. and Kristin |date=May 19, 2016 |title=U.S.-EU Data Privacy: From Safe Harbor to Privacy Shield |url=https://sgp.fas.org/crs/misc/R44257.pdf |journal=Congressional Research Service}} Directive 95/46/EC declares in Chapter IV Article 25 that personal data may only be transferred from the countries in the [[European Economic Area]] to countries which provide [[adequate]] privacy protection. Historically, establishing adequacy required the creation of national laws broadly equivalent to those implemented by Directive 95/46/EU. Although there are exceptions to this blanket prohibition – for example where the disclosure to a country outside the EEA is made with the consent of the relevant individual (Article 26(1)(a)) – they are limited in practical scope. As a result, Article 25 created a legal risk to organizations which transfer personal data from Europe to the United States.
The program regulates the exchange of [[passenger name record]] information between the EU and the US. According to the EU directive, personal data may only be transferred to third countries if that country provides an adequate level of protection. Some exceptions to this rule are provided, for instance when the controller themself can guarantee that the recipient will comply with the data protection rules.
The [[European Commission]] has set up the "Working party on the Protection of Individuals with regard to the Processing of Personal Data," commonly known as the "Article 29 Working Party". The Working Party gives advice about the level of protection in the [[European Union]] and third countries.{{Cite web|title=EPIC – Article 29 Working Party|url=https://epic.org/privacy/art29wp/#:~:text=The%20Working%20Party%20on%20the,Member%20States,%20the%20European%20Data|access-date=2021-03-20|website=epic.org|language=en|url-status=live|archive-url=https://web.archive.org/web/20210815003317/https://epic.org/privacy/art29wp/|archive-date=15 Aug 2021}}
The Working Party negotiated with U.S. representatives about the protection of personal data, the [[Safe Harbor Principles]] were the result. Notwithstanding that approval, the self-assessment approach of the Safe Harbor remains controversial with a number of European privacy regulators and commentators.{{cite web |url=http://ec.europa.eu/justice_home/fsj/privacy/docs/adequacy/sec-2004-1323_en.pdf |title=SEC (2004) 1323: The implementation of Commission Decision 520/2000/EC on the adequate protection of personal data provided by the Safe Harbour privacy Principles and related Frequently Asked Questions issued by the US Department of Commerce |publisher=[[European Commission]] |url-status=dead |archive-url=https://web.archive.org/web/20060724173657/http://ec.europa.eu/justice_home/fsj/privacy/docs/adequacy/sec-2004-1323_en.pdf |date=20 October 2004 |archive-date=24 July 2006 }}
The Safe Harbor program addresses this issue in the following way: rather than a blanket law imposed on all organizations in the [[United States]], a voluntary program is enforced by the [[Federal Trade Commission]]. U.S. organizations which register with this program, having self-assessed their compliance with a number of standards, are "deemed adequate" for the purposes of Article 25. Personal information can be sent to such organizations from the EEA without the sender being in breach of Article 25 or its EU national equivalents. The Safe Harbor was approved as providing adequate protection for personal data, for the purposes of Article 25(6), by the European Commission on 26 July 2000.{{cite web|url=http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=CELEX:32000D0520:EN:HTML |title=2000/520/EC: Commission Decision of 26 July 2000 pursuant to Directive 95/46/EC of the European Parliament and of the Council on the adequacy of the protection provided by the safe harbour privacy principles and related frequently asked questions issued by the US Department of Commerce |work=[[Official Journal of the European Union]], L Series |volume=215 |pages=7–47 |via=[[Eur-Lex]] |date=25 August 2000 }}
Under the Safe Harbor, adoptee organizations need to carefully consider their compliance with the ''onward transfer obligations'', where [[personal data]] originating in the EU is transferred to the US Safe Harbor, and then onward to a third country. The alternative compliance approach of "[[binding corporate rules]]", recommended by many EU privacy regulators, resolves this issue. In addition, any dispute arising in relation to the transfer of HR data to the US Safe Harbor must be heard by a panel of EU privacy regulators.{{cite web |url=http://ec.europa.eu/justice_home/fsj/privacy/docs/adequacy/information_safe_harbour_en.pdf |title=Q&A on the European Data Protection Authorities Panel foreseen by the Safe Harbour Decision |publisher=[[European Commission]] |url-status=dead |archive-url=https://web.archive.org/web/20060724174212/http://ec.europa.eu/justice_home/fsj/privacy/docs/adequacy/information_safe_harbour_en.pdf |archive-date=2006-07-24 }}
In July 2007, a new, controversial, [[Passenger Name Record]] agreement between the US and the EU was made.{{cite web|title=New EU-US PNR Agreement on the processing and transfer of Passenger Name Record (PNR) data – CHALLENGE | Liberty & Security|url=http://www.libertysecurity.org/article1591.html|url-status=usurped|archive-url=https://web.archive.org/web/20120112021643/http://www.libertysecurity.org/article1591.html|archive-date=12 January 2012|access-date=11 January 2022|website=libertysecurity.org}} A short time afterwards, the [[Presidency of George W. Bush|Bush administration]] gave exemption for the [[Department of Homeland Security]], for the [[Arrival and Departure Information System]] (ADIS) and for the [[Automated Target System]] from the [[1974 Privacy Act]].[[Statewatch]], [http://www.statewatch.org/news/2007/sep/04eu-usa-pnr-exemptions.htm US changes the privacy rules to exemption access to personal data] September 2007
In February 2008, [[Jonathan Faull]], the head of the EU's Commission of Home Affairs, complained about the US bilateral policy concerning PNR.[http://euobserver.com/9/25657 Brussels attacks new US security demands], European Observer. See also [http://www.statewatch.org/news/ Statewatch newsletter] February 2008 The US had signed in February 2008 a memorandum of understanding (MOU) with the [[Czech Republic]] in exchange of a visa waiver scheme, without concerting before with Brussels.[http://www.rue89.com/2008/03/04/a-divided-europe-wants-to-protect-its-personal-data-wanted-by-the-us A divided Europe wants to protect its personal data wanted by the US] {{Webarchive|url=https://web.archive.org/web/20110522052052/http://www.rue89.com/2008/03/04/a-divided-europe-wants-to-protect-its-personal-data-wanted-by-the-us |date=2011-05-22 }}, ''[[Rue 89]]'', 4 March 2008 {{in lang|en}} The tensions between Washington and Brussels are mainly caused by a lesser level of data protection in the US, especially since foreigners do not benefit from the US [[Privacy Act of 1974]]. Other countries approached for bilateral MOU included the United Kingdom, Estonia, Germany and Greece.[[Statewatch]], March 2008
== Technical measures == {{multiple issues|section=yes|{{mcn section|date=July 2024}} {{update|date=July 2024}}}} There are [[Privacy#Techniques to improve privacy|techniques to improve privacy]], [[privacy-enhancing technologies]], and [[privacy software]] tools. People building and updating systems can use [[privacy by design]] and [[privacy engineering]] strategies and techniques. For example, by converting data into a non-readable format, [[encryption]] prevents unauthorized access.
==See also== {{columns-list|colwidth=30em|
- [[Genetic privacy]]
- [[Pirate Party]]
- [[Privacy]]
- [[Privacy by design]]
- [[Privacy enhancing technologies]]
- [[Privacy law]]
- [[Privacy software]]
- [[Right to be forgotten]]
- [[Web literacy]] (privacy) }}
;Computer science specific {{columns-list|colwidth=30em|
- [[Authentication]]
- [[CIA triad]]
- [[Outline of computer security]]
- [[Data security]]
- [[Data sovereignty]]
- [[Data localization]]
- [[Digital inheritance]]
- [[Digital self-determination]]
- [[ePrivacy Regulation]]
- [[Data loss prevention software]]
- [[Data retention]]
- [[Differential privacy]] }}
;Organisations {{columns-list|colwidth=30em|
- [[Confederation of European Data Protection Organisations]]
- [[Data Privacy Day]] (28 January)
- [[International Association of Privacy Professionals]] (headquartered in USA)
- [[Privacy International]] (headquartered in UK) }}
;Scholars working in the field {{columns-list|colwidth=30em|
- [[Adam Back]]
- [[Cynthia Dwork]]
- [[Helen Nissenbaum]]
- [[Ian Goldberg]]
- [[Khaled El Emam]]
- [[Latanya Sweeney]]
- [[Peter Gutmann (computer scientist)|Peter Gutmann]]
- [[Stefan Brands]] }}
==References== {{Reflist|30em}}
==Further reading== {{Library resources box}}
- {{cite book|author1=Philip E. Agre|author2=Marc Rotenberg|title=Technology and privacy: the new landscape|year=1998|publisher=MIT Press|isbn=978-0-262-51101-8|url-access=registration|url=https://archive.org/details/technologyprivac0000agre}}
- {{cite book |last1=Koopman |first1=Colin |title=How We Became Our Data: A Genealogy of the Informational Person |date=2019 |publisher=University of Chicago Press |location=Chicago |isbn=9780226626581}}
==External links== ;International
- [https://web.archive.org/web/20120111162553/http://www.echr.coe.int/NR/rdonlyres/4FCF8133-AD91-4F7B-86F0-A448429BC2CC/0/FICHES_Protection_des_données_EN.pdf Factsheet on ECtHR case law on data protection]
- [https://web.archive.org/web/20190904150616/https://icdppc.org/ International Conference of Data Protection and Privacy Commissioners]
- [https://web.archive.org/web/20120418083909/http://www.biometricsinstitute.org/pages/privacy-biometrics.html Biometrics Institute Privacy Charter]
;Europe
- [http://ec.europa.eu/justice_home/fsj/privacy/ EU data protection page]
- [http://unescoprivacychair.urv.cat/ UNESCO Chair in Data Privacy]
- [http://www.edps.europa.eu/EDPSWEB/ European Data Protection Supervisor] {{Webarchive|url=https://web.archive.org/web/20081219153008/http://www.edps.europa.eu/EDPSWEB/ |date=2008-12-19 }}
;Latin America
- [https://web.archive.org/web/20130108061616/http://www.rlpdp.com/ Latin American Data Protection Law Review]
;North America
- [http://www.pacc-ccap.ca/ Privacy and Access Council of Canada]
- [http://privacy.cs.cmu.edu/ Laboratory for International Data Privacy] {{Webarchive|url=https://web.archive.org/web/20190812043133/http://privacy.cs.cmu.edu/ |date=2019-08-12 }} at [[Carnegie Mellon University]].
- [http://www.epic.org/privacy/consumer/states.html Privacy Laws by State]
;Journals
- [http://www.computer.org/security/ IEEE Security & Privacy magazine]
- [http://www.tdp.cat/ Transactions on Data Privacy]
{{Data}} {{Privacy}} {{Authority control}}
[[Category:Information privacy| ]] [[Category:Data laws]] [[Category:Data protection]] [[Category:Privacy]]
Related Articles
From MOAI Insights

디지털 트윈, 당신 공장엔 이미 있다 — 엑셀과 MES 사이 어딘가에
디지털 트윈은 10억짜리 3D 시뮬레이션이 아니다. 지금 쓰고 있는 엑셀에 좋은 질문 하나를 더하는 것 — 두 전문가가 중소 제조기업이 이미 가진 데이터로 예측하는 공장을 만드는 현실적 로드맵을 제시한다.
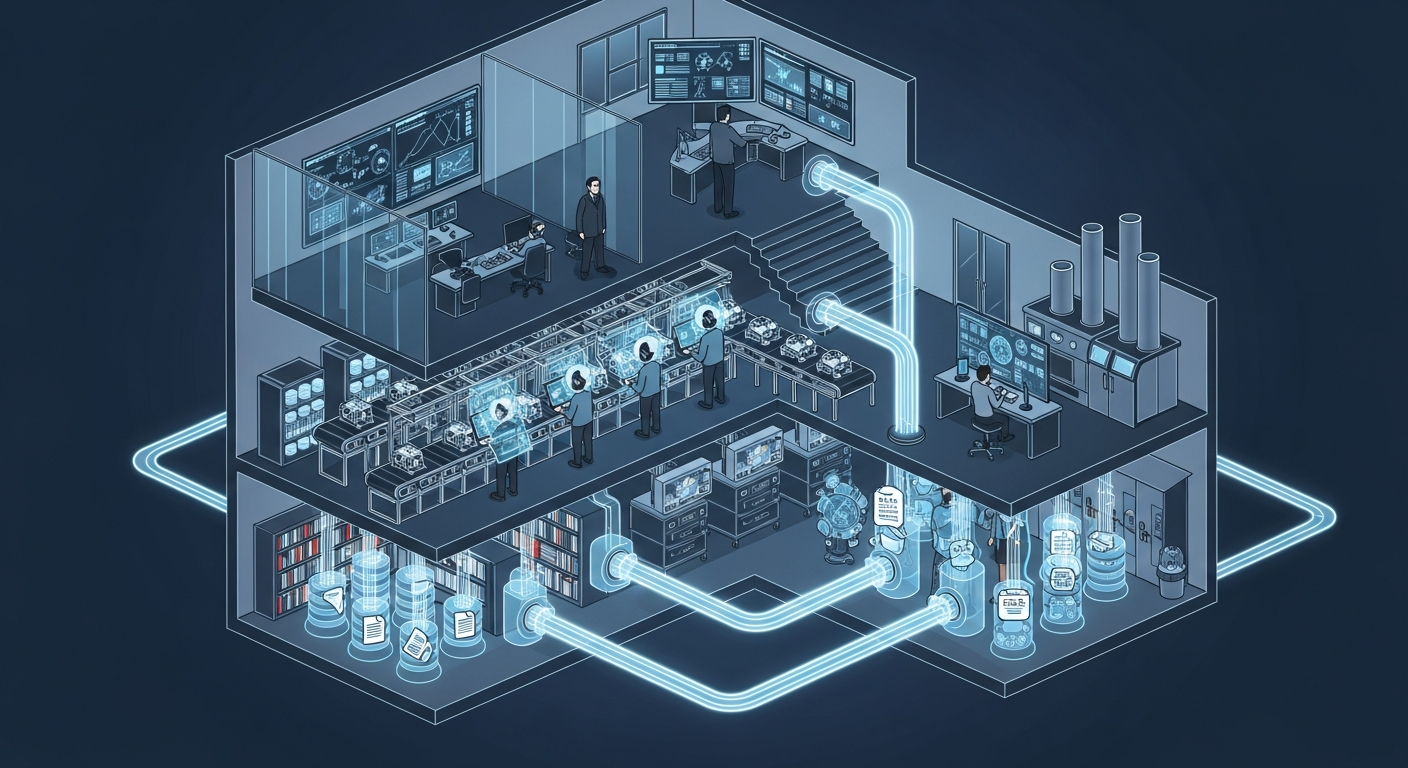
공장의 뇌는 어떻게 생겼는가 — 제조운영 AI 아키텍처 해부
지식관리, 업무자동화, 의사결정지원 — 따로 보면 다 있던 것들입니다. 제조 AI의 진짜 차이는 이 셋이 순환하면서 '우리 공장만의 지능'을 만든다는 데 있습니다.

그 30분을 18년 동안 매일 반복했습니다 — 품질팀장이 본 AI Agent
18년차 품질팀장이 매일 아침 30분씩 반복하던 데이터 분석을 AI Agent가 3분 만에 해냈습니다. 챗봇과는 완전히 다른 물건 — 직접 시스템에 접근해서 데이터를 꺼내고 분석하는 AI의 현장 도입기.
Want to apply this in your factory?
MOAI helps manufacturing companies adopt AI tailored to their operations.
Talk to us →